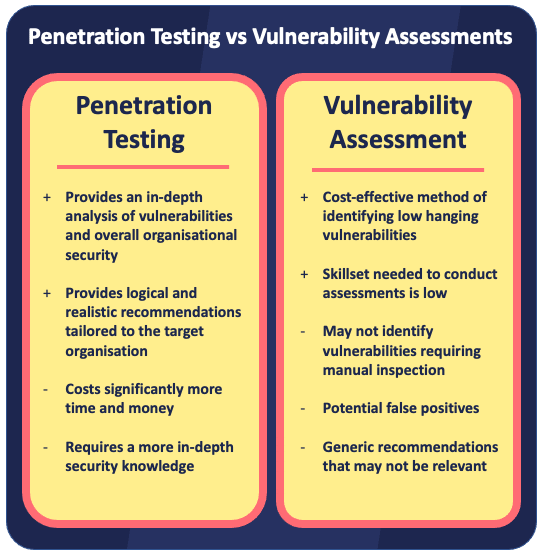
It can be easy to mistake vulnerability assessments and penetration testing as the same service. The chronic misbranding of vulnerability assessments as penetration tests within the security industry has led to a blurring of lines between the two services. In this blog we look at what makes each service different and discuss their pros and cons.
What is a Vulnerability Assessment?
In its simplest form a vulnerability assessment is a scan that attempts to identify vulnerabilities and weaknesses in your IT infrastructure. The scan uses a list of pre-configured vulnerability signatures (indicators) to probe the networks, systems and applications being tested. So, you could think of vulnerability assessments as an automated evaluation of your systems’ security where the main goal is to identify the low hanging vulnerabilities and to provide recommendations to help you fix these.
A vulnerability assessment can be a very cost-effective way of identifying vulnerabilities, however, it will likely miss vulnerabilities requires a logical inspection that currently only expert manual testing can provide. Vulnerability assessments can also generate an overwhelming amount of information that often contains false positives. This can sometimes make the output hard to digest by non-security professionals and render some recommendations unreliable.
What is a Penetration Test?
A penetration test is a more in-depth assessment conducted by a skilled security professional. It involves the tester manually testing networks, systems and applications to try and achieve a primary goal such as breaching an external network perimeter and compromising the domain or gaining access to specific data. As a secondary objective, the tester will attempt to identify and exploit vulnerabilities to validate that they exist and measure the impact if the vulnerabilities were to be exploited by attackers.
It must be noted that penetration tests will usually include some level of vulnerability scanning as part of the initial vulnerability discovery process. However, this will be a relatively minor part of the engagement.
Penetration testing will cost more than a vulnerability assessment; however, it offers a level of security testing that vulnerability assessments cannot currently match. It can help you better understand how an attacker might attempt to compromise your security and offers more thorough recommendations on how to secure your organisation.
What Type of Testing is Right for You?
Determining the right service for your organisation will depend on your budget, risk appetite, the maturity of your security posture and what objectives you have. If you’ve not performed any security testing before, a vulnerability assessment would be a logical and cost-effective first step to quickly identify and address common vulnerabilities.
A penetration test could provide an additional layer of security assurance and vulnerability coverage. A penetration test is often critically important where you hold highly sensitive data, have a high profile, or have a complex IT infrastructure, however, penetration testing can also be valuable to companies of all sizes and IT maturity.
Both vulnerability assessments and penetration tests are a snapshot in time of your security posture. As your IT infrastructure changes, the threat landscape evolves and new vulnerabilities emerge, so your security will need to be re-tested. It’s for this reason that many organisations will conduct regular testing to give them an ongoing understanding of their vulnerabilities. It’s not uncommon for these companies to have penetration testing conducted annually and to supplement this with quarterly vulnerability assessments.
All organisations should aim to put in place a testing plan tailored to their specific needs and requirements, and that also takes account of any budget constraints.
If you would like to discuss what security testing solution is best for your organisation, please get in touch for a free consultation.




